Author: Andrew


Windows 10 very close to End of Life
If you support friends and family with their computer use like me, what are you looking to do after October…

Apple, MacOS, Old Machines, Hackintosh’s & Other Stuff
I still have a love-hate relationship with Apple equipment. Sure, I’ve gone from a Hater (based on Hardware Value for…
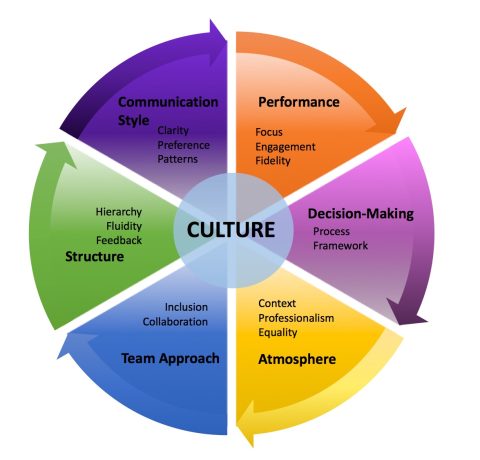
Company Culture
Company Culture is something that almost every company wants to get right, so how do you do that? Avoid the…

How I Avoid “Phone Network” Scammers
I have several mobile phone numbers, but they all have one thing in common. While they are on the same…

New FireWall replaces PiHole & Providers Router
I’ve recently updated my internet stack, which is now as follows: 2000Mbps Fibre to the Premises (Symmetric 2Gbps Up &…
Deauth Detector, the new must have.
Despite being a security-oriented government agency, a company I’ve been working for recently provided me with a Wi-Fi-only laptop. Usually,…
Companies: Should they offer you less than your requested minimum?
One of the first things that Recruitment Agents ask is what remuneration I am looking for, and they often ask,…
Online Tools for Techies
DNS Tools DNS Configuration Check https://intodns.com/ The Defacto DNS configuration check and guidelines. IP Addresses ifconfig.co https://ifconfig.co Determine your…

Human attributes that cannot be replaced, yet, by AI
With AI being adopted a little too fast, it’s probably a good idea to leverage skills that AI cannot replace…